As iPhones have become a ubiquitous part of daily life, the privacy and security of these devices have become increasingly important, especially your Apple ID.
One of the most concerning issues is the possibility of someone else gaining remote access to your phone, allowing them to monitor your activities and steal sensitive information, such as social media accounts, security information, passwords, files, logs, and other account data, from your Apple account.
The thought of someone else accessing your private data can be frightening, and many iPhone users may not even realize that their phone has been compromised.
Therefore, it’s important to understand the signs that your phone may have been hacked and what steps you can take to protect yourself with the security features.
In this article, we will explore the methods that someone could use to remotely access your phone and what you can do to find out if your device has been compromised. We will also discuss the steps you can take to secure your phone and prevent future hacking attempts.
How Can Someone Access an iPhone Remotely?
Remote access to someone’s phone has become increasingly common with the advancement of technology.
As our phones store a vast amount of personal information, including contacts, messages, photos, and sensitive data, protecting our devices from unauthorized access is crucial.
There are several ways that someone can remotely access your phone, including hacking and spyware.
These methods allow them to obtain your personal information without your knowledge, leading to serious privacy and security concerns.
Understanding these methods and how to prevent them from keeping your phone and personal data safe is essential. So here are the most common ones.
#1 Malicious Software

Malicious apps can be downloaded onto your phone without your knowledge, allowing a remote attacker to take control of your device. These apps can be disguised as legitimate apps, making it difficult to detect these apps installed.
#2 Phishing
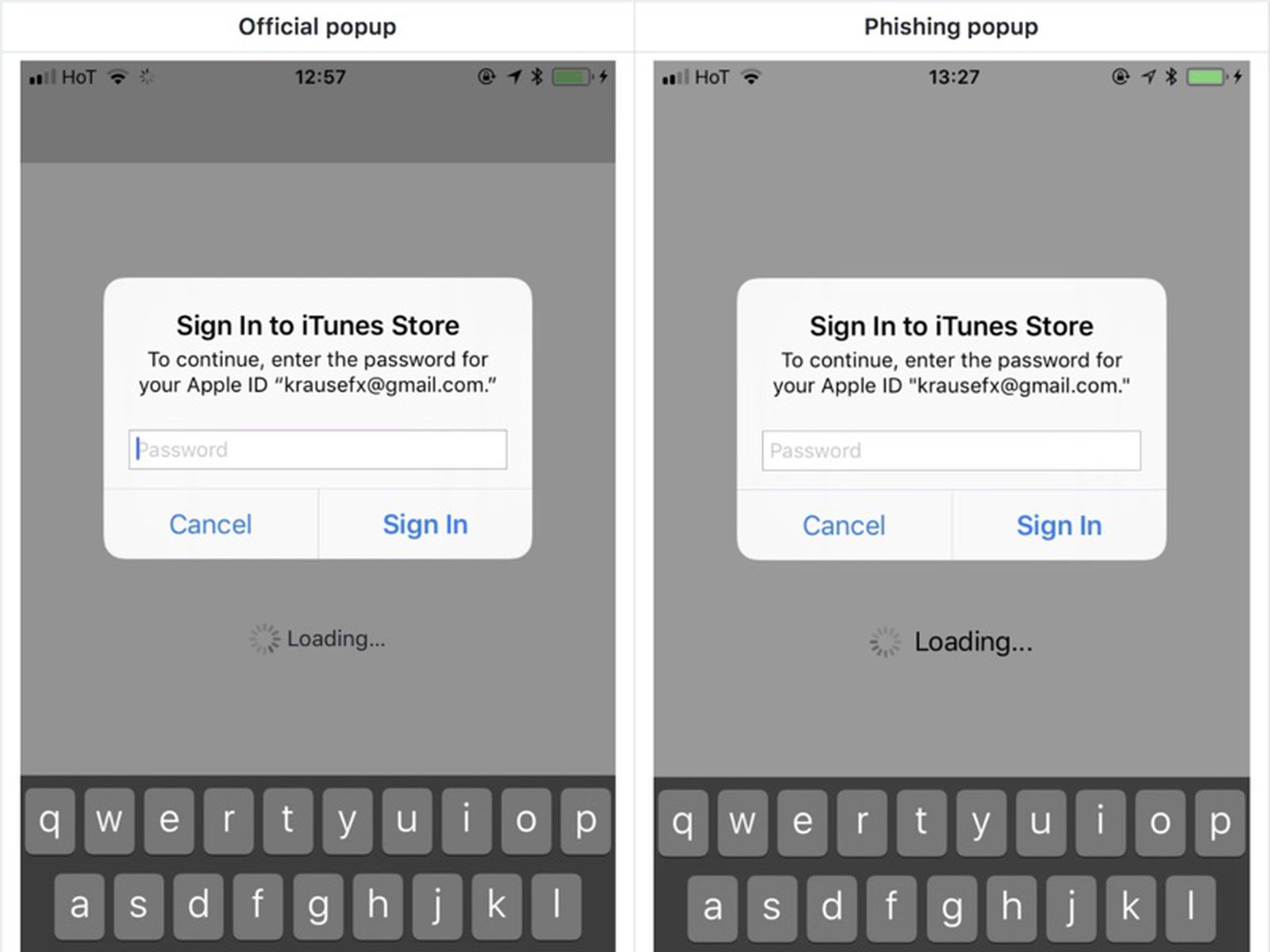
Phishing attacks involve sending an email or text message that appears to be from a legitimate source, such as your bank or social media account but is actually from an attacker.
The message may contain a link that, when clicked, downloads a malicious app or allows the attacker to access your iPhone remotely.
#3 Public Wi-Fi Networks

Public Wi-Fi networks are often unsecured, making it easy for attackers to intercept your data and gain access to your device. They can also create fake public Wi-Fi networks that appear to be legitimate, tricking you into connecting to them and giving them access to your phone.
In most cases, the hacker won’t even need physical access to your iPhone.
#4 Social Engineering
Social engineering is the art of manipulating people into divulging confidential information. Attackers may call or email you pretending to be someone else, such as a bank representative, and ask for your login credentials or other personal information.
Stop right there if you can’t recognize who’s talking to you.
#5 Software Vulnerabilities

Attackers can exploit software vulnerabilities to gain remote access to your device. These vulnerabilities may exist in your iPhone operating system, social media apps, or other software.
Obviously, these are the beginning of more signs you’ll probably notice.
Signs There Might Be a Remote Access Tool Running On Your Phone
Signs your Apple device has been targeted can vary, but this list should be enough for you to start questioning it. Here are 10 common signs that your phone may have been hacked or is being monitored:
- Battery drains quickly: If your phone’s battery drains faster than usual, it may be a sign that some app or program is running in the background without your knowledge. This is especially suspicious if you haven’t downloaded any new apps recently.
- Higher data usage: If your phone’s data usage is much higher than usual, it could be a sign that something is running in the background, such as a spyware app, which uses more data than normal.
- Unknown apps: If you see any unknown or suspicious apps on your phone that you didn’t download yourself, it may be a sign that your phone has been hacked or infected with malware.
- Strange pop-ups: If you start seeing pop-ups on your phone that you can’t explain or that ask for unusual permissions, it could be a sign that someone is trying to install spyware or malware on your device.
- The phone behaves abnormally: If your phone starts behaving in unusual ways, such as taking longer than usual to turn on or off, randomly shutting down, having problems with your iCloud account or iCloud backup, or making strange noises, it may be a sign that it has been compromised.
- Unexplained charges: If you see any unexplained charges on your phone bill, it could be a sign that your iPhone has been remotely accessed.
- Suspicious text messages or emails on your iPhone screen: If you receive any suspicious text messages or emails, especially those that ask for personal information or passwords, it could be a sign that someone is trying to hack into your phone.
- Unusual background noise: If you hear unusual background noise during phone calls, it could indicate that someone is listening to your conversations.
- Phone heats up: If your phone heats up more than usual, it may be a sign that some app or program is running in the background without your knowledge, which could be a sign of malware or spyware.
- Passwords don’t work: If your passwords suddenly stop working, it could be a sign that someone has accessed your accounts and changed your login credentials.
It’s important to note that these signs do not always mean that your phone has been hacked or is being monitored, but they should serve as a warning to take action to secure your device and protect your personal information.
Now, let’s learn what we can do to prevent and fix the problem in case you’re suspicious.
What to Do to Prevent Hackers and Fix Your Phone
Suppose you’ve been concerned that some unusual and potentially harmful tracking software might be installed on your iOS devices, only to find that the situation wasn’t as dire as you feared.
In light of this, here’s a concise, step-by-step guide to help you safeguard your device against any future threats.
Preventing Potential Future Attacks on Your iPhone

- Keep your phone’s software up to date: Make sure you have installed the latest version of your phone’s operating system. This will ensure that your phone has the latest security updates and patches. Remember to install each and every official update.
- Install anti-malware software: Download and install reputable anti-malware software on your phone. This will help protect your phone against malicious apps that could be used for spying as an extra layer of security.
- Be careful when downloading apps: Only download apps from Apple App Store. Read app reviews and check the app permissions before downloading.
- Avoid clicking on suspicious links: Do not click on links from unknown sources or suspicious emails. These links could lead to the installation of malware on your phone.
- Use a strong password: Use strong passwords and enable two-factor authentication whenever possible to prevent unauthorized access to your phone.
- Turn off unnecessary features: Turn off features like Bluetooth and Wi-Fi when not in use to prevent hackers from accessing your phone through these channels.
- Be cautious when connecting to public Wi-Fi: Avoid using public Wi-Fi networks as they are often unsecured and could be used to spy on your phone. The same goes to public chargers or public charging stations.
- Review app permissions: Regularly review app permissions on your phone and disable access to features that are not necessary for the app to function.
- Check for unusual activity: Keep an eye out for unusual activity on your phone, such as new apps, messages, or calls you did not initiate.
- Reset your phone: If you suspect it has been compromised, reset it to its factory settings. This will erase all data on your phone, including any spy apps that may have been installed.
Now, if you are actually convinced there is a spying app or something like that monitoring your phone, here are the best things you can try to solve the issue.
Solving Undesired Remote Access to Your iPhone

- Conduct a full scan: First, you should scan your phone for any malware or spy apps. There are various anti-virus and anti-spyware apps available that can help you with this.
- Change your passwords: Avoid the same password. If you suspect someone has been accessing your phone, they may have also gained access to your passwords. Change all your passwords, including those for your email, social media, and banking apps.
- Check your app permissions: Go through the app permissions on your phone and see if any apps can access your microphone, camera, or other sensitive data. If you find anything suspicious, revoke the permission.
- Update your phone: Ensure your phone’s operating system and apps are current. Security updates are released regularly to fix any vulnerabilities that hackers and spy apps can exploit. You can also ask for Apple Support if you’ve been hacked remotely.
- Disable or uninstall suspicious apps: If you find any suspicious apps on your phone, disable or uninstall them. Some spy apps are designed to be hidden, so it’s important to be vigilant. Also, be careful following onscreen instructions from apps if you’re unsure what they are.
- Factory-reset your phone: As a last resort, you can reset your phone to its factory settings. This will erase all the data on your phone, including any spy apps. Make sure to back up all your important data before resetting your phone.
- Monitor your phone: After taking these steps, monitor your phone closely to ensure that suspicious activity has stopped. If you notice any further signs of hacking or spying, take immediate action to protect your phone and your privacy.

By following these steps, you can take control of your phone’s security and protect yourself from unwanted spying and hacking. Remember to stay vigilant and take action if you suspect that your phone has been compromised.
Add comment