Imagine this: your trusty smartphone, always by your side, could be hacked just by someone knowing your phone number.
Sounds like a scene from a gripping spy thriller, doesn’t it?
Buckle up because we’re about to explore this scary possibility in this article.
You may recall from the previous articles we’ve given you a sneak peek into the world of spying apps and even presented you with our pick of the 21 Best Tracking Apps to use in 2023.
Tracking apps are handy for anyone who’s considering tracing a mobile device, but keep in mind these apps require more than just a phone number to function.
So, this piques our curiosity: Could someone truly infiltrate your phone armed only with your number?
Let’s delve in, shall we?
Phone Hacking with Just Your Number: Truth or Myth?

The answer is more complex than you’d think.
Yes, expert hackers need just your phone number to infiltrate your cell phone and access your online accounts, but the phone number is merely the first step.
To deceive individuals, hackers utilize a blend of time-tested strategies and sophisticated technical expertise.
Here’s a rundown of hackers’ most frequent tactics to compromise your Android phone or iPhone.
The Art of Phishing Links
You’d agree that if a hacker has your number, they have a direct line to you, right? Here is how phishing links work.
They typically craft an email, SMS, or Whatsapp message posing as a reputable entity like your bank.
These emails can look extremely professional and may alarm you with news of an unexpected windfall or prize that’s almost yours.
You just need to click on a link to claim your bounty.
Clicking on the link will lead you to a sham website where you’ll be asked to enter your private details to continue.
The information requested could include your bank account information, social media profiles, and any other data you possess that could be of value to the hacker.
The Game of Phishing Scams (Think Phone Calls)

While it seems akin to phishing links, there’s a subtle difference.
Phishing scams are a form of manipulation known as social engineering, with the aim being to earn someone’s trust to access their personal data for selfish gains.
In other words, these scams don’t necessarily come via email or text messages. Hackers employ various inventive and varied tactics, including phone calls, bogus Wi-Fi networks, malicious apps, and more.
For example, A hacker might call your phone, impersonate your service provider, and request sensitive details that seem reasonable to provide in that context.
This method is a particularly easy way to trick unsuspecting folks, especially the elderly, into revealing crucial information.
The Trick of Phone Number Duplication to Reset Your Passwords

Talented hackers have a nifty trick up their sleeves – they can duplicate your phone number.
Imagine the consequences if the attacked phone number is linked to critical accounts such as your social media or bank accounts.
Hackers typically use this cloned number to intercept OTPs (one-time passwords) or verification codes and gain access to your login credentials.
In other words, they can hit the “Forgot Password?” button and reset your account.
It’s worth noting that many folks don’t employ two-factor authentication for their account passwords, which can make their accounts vulnerable.
And speaking of vulnerabilities, let’s talk about the issue of weak passwords.
According to a study by Nord, the five most common passwords used in the United States are surprisingly easy to crack. Here’s a rundown of them, along with the time it takes to break each one:
- ‘guest’ → 10 seconds
- ‘123456’ → < 1 second
- ‘password’ → < 1 second
- ‘12345’ → < 1 second
- ‘a1b2c3’ → < 1 second
I think we can agree that stronger passwords could really come in handy here, right?
Ultimately, while a hacker would need more than just your number to infiltrate your phone, knowing your number certainly could give them a head start.
So, let’s not make their job any easier, shall we?
The Web of Malicious Websites
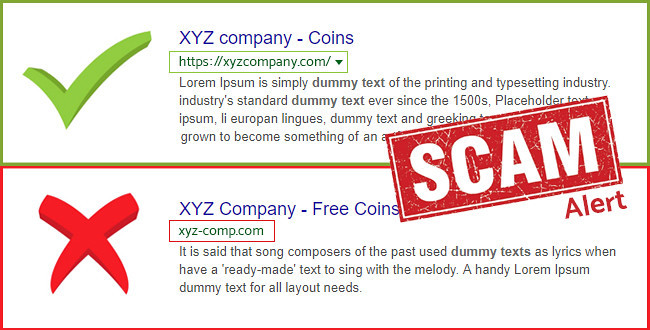
Let’s face it: we all have our favorite online haunts – from gaming sites to betting platforms and more.
Unfortunately, hackers capitalize on these interests by creating bogus websites that offer alluring downloads. These downloads might seem harmless, but lurking within them can be malicious software waiting to pounce.
Hackers score an unauthorized ticket into your phone once you innocently click on these deceptive links to download the content.
Suddenly, your data and privacy are hanging by a thread.
The Devious Strategy of SIM Swapping

SIM swapping is a crafty method hackers use to hijack your phone.
It involves tricking the mobile carrier into transferring your phone number onto a SIM card that the hacker controls.
With the SIM card swapped, the hacker starts receiving all calls, text messages, and authentication codes that were meant for you.
The sneaky dance of SIM swapping begins with the hacker collecting details about you, such as your phone number, personal details, bank account info, and carrier details.
Armed with this information, they contact your mobile carrier, convincingly impersonating you or providing enough data to seem legit, and request a SIM card transfer.
Once the switch is successful, the hacker uses your phone number to sidestep security measures and commandeer your accounts.
The Illusion of Security?
You might feel secure thinking that you’re not an easy mark just because you’re careful with your personal information, are well-versed in mobile security, or keep your banking data on a separate phone, right?
Well, here’s a reality check: Hackers can do a whole lot more with the data stored on your mobile device than you might imagine.
Ready to explore? Let’s dive in.
The Potential Hazards When a Hacker Infiltrates Your Phone
Whether you’re an Android enthusiast or an iPhone devotee, it’s a safe bet that your device holds a treasure trove of personal data.
And it’s not just banking apps – there are a host of other data nuggets that can be used against you and even sold online.
Let’s delve into the kind of valuable information that might be at risk.
Your Credit History Laid Bare
Even if you don’t have a banking app installed on your phone, you could still be logged into websites or apps that monitor your financial status.
These platforms would have details like your outstanding debt, your checking account balance, and who your creditors are.
This kind of information is like catnip to ill-intentioned individuals looking to pilfer your data for their nefarious ends.
Social Media Accounts: A Playground for Identity Thieves

We all know someone who’s making a living off their YouTube channel or online business.
If a hacker gains access to your social media, they could impersonate you and even request money from your friends and family. It’s not just an invasion of privacy – it’s full-on identity theft.
And because your loved ones would think they’re helping you, these phishing messages can be devastatingly effective.
Physical Threats in the Real World
While it may sound like something out of a spy movie, there have been real-life cases where hackers have infiltrated a phone to uncover someone’s location and daily routines.
This situation could leave you vulnerable to threats in the real world, emphasizing how crucial it is to take active steps to ensure your privacy and secure your personal information.
Now that you have an idea of how hackers can break into your phone let’s explore some strategies to keep these digital intruders at bay.
How to Prevent Hackers from Accessing My Cell Phone

Let’s split these security features into two categories.
The idea is to show you how you can take simple steps to protect your data and count on technology to answer your security questions.
Simple Measures to Protect Your Phone
- Don’t disclose your mobile number on websites and forums.
- Don’t click on any malicious links when you receive suspicious messages.
- Don’t answer unsolicited calls.
- Don’t keep bank statements on your phone.
- Don’t give physical access to your phone to strangers.
- Don’t install suspicious apps.
- Stay alert for unusual activity on your accounts.
- Block numbers repeatedly make unwanted calls to you.
- Activate two-factor authentication for your online accounts.
- Change passwords immediately after noticing unusual activities on your accounts.
Use Technology to Protect Your Phone
In the broad landscape of digital security, there are countless tools and apps to protect your phone from threats and unauthorized access.
But let’s keep things simple. We’ll focus on two straightforward yet powerful technologies that can effectively safeguard your phone.
Antivirus Apps to the Rescue
Antivirus software is like your phone’s personal bodyguard. It tirelessly scans and scrutinizes the apps on your device, ever-watchful for any hint of foul play.
If it spots an app that seems suspicious or potentially harmful, it jumps into action, either isolating the app or marking it for removal.
The Power of a Factory Reset
A factory reset is like a deep cleanse for your phone. It scrubs away harmful apps, resetting your device back to its pristine state – just like when you first took it out of the box.
If you’re regularly getting messages that raise red flags or have a hunch that a malicious app might lurk on your phone, a factory reset can be your superhero, swooping in to save the day.
Important Note: A factory reset will wipe out everything on your phone – all your apps and all their associated files. It’s like hitting the delete button on your device’s data. So, it’s really important that you back up your stuff before you go ahead with a factory reset.
Now that you know how to take your device’s security to the next level, let’s head to the conclusion.
Wrapping It Up

Your phone number is more than just a string of digits – it’s a portal to your digital universe.
You can armor up your Android or iPhone against potential hackers by taking straightforward but key steps like crafting strong passwords, turning on two-factor authentication, and choosing reliable antivirus software.
Protecting your device means shielding your personal details, texts, and financial records, but it’s also about defending yourself from the specter of identity theft.
Don’t let someone else take the wheel of your iPhone or Android; instead, equip yourself with the knowledge and proactive steps to keep your digital world locked up tight.
Stay on your toes, and stay secure
Frequently Asked Questions

Can hackers worm their way into my phone with just my phone number?
No, hackers can’t bust into your phone with only your phone number. However, they can use your number as a stepping stone in a bunch of crafty techniques, like SIM swapping, to unlawfully access your device and accounts.
How do hackers get their hands on my phone numbers?
Hackers have a bag of tricks to snag your phone numbers. They might exploit data breaches, use social engineering tactics, or take advantage of weaknesses in online platforms and services.
Do hackers need to get their hands on my phone to hack it?
Not always. While some sneaky moves might require them to install malicious software on your device, others, like SIM swapping and phishing, can be pulled off from afar, without needing to touch your phone.
Can hackers use Wi-Fi connections to infiltrate my device?
Indeed, Wi-Fi connections can be a chink in your armor.
Sticking to secure Wi-Fi networks and steering clear of public or untrusted ones is important to lower your risk of unauthorized access.
Can hackers use people search sites to dig up my personal details?
Absolutely, people search sites can be a goldmine for hackers looking for info about their next victim. It’s crucial to be careful about what you share online and to tweak your privacy settings on social media and other online platforms.
Add comment